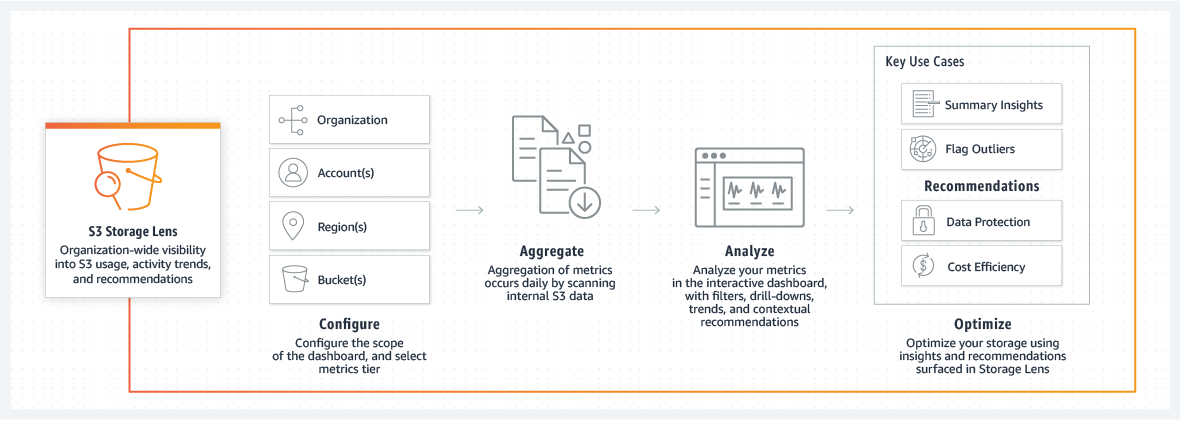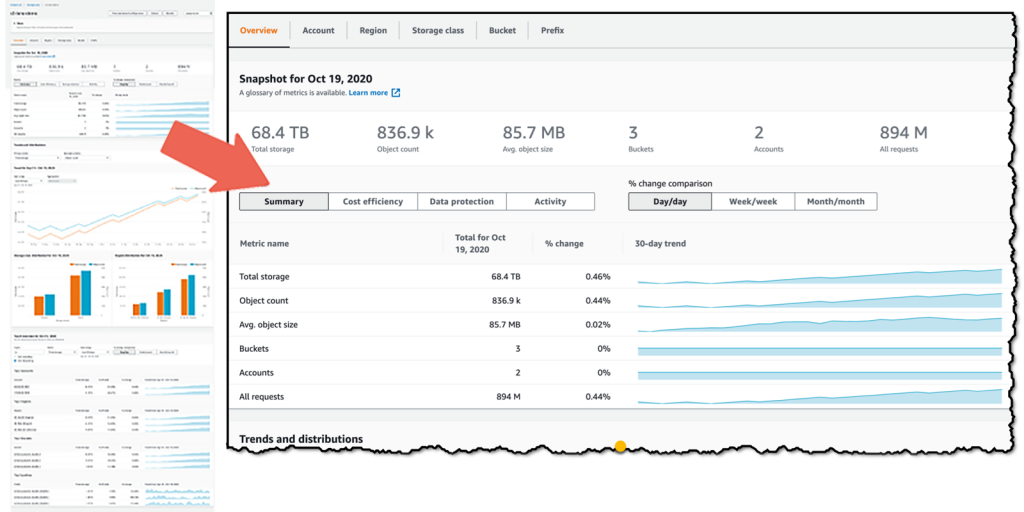
Introducing Amazon S3 Storage Lens – Organization-wide Visibility Into Object Storage | AWS News Blog

How to Protect Your Web Application Against DDoS Attacks by Using Amazon Route 53 and an External Content Delivery Network | AWS Security Blog
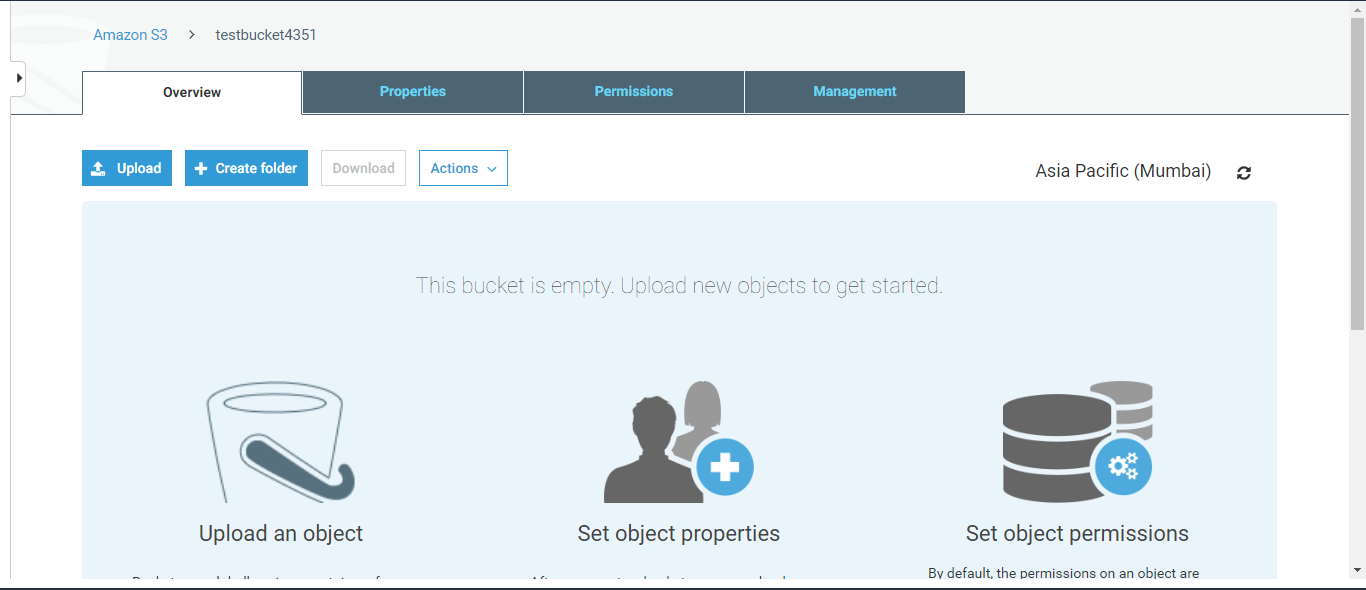
How To Protect Objects From Accidental Deletion And Overwrite Using S3 Object Versioning | by Deepak Surendran | Tensult Blogs | Medium

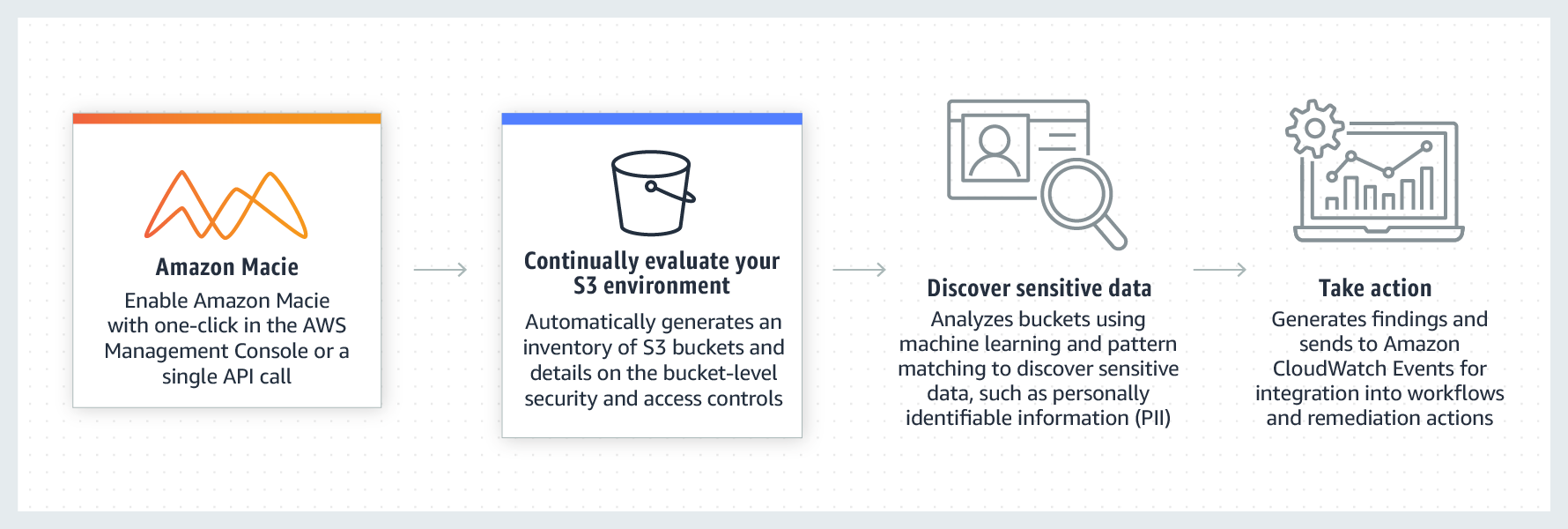
Employing Amazon Macie to Discover and Protect Sensitive Data in your Amazon S3-based Data Lake | Programmatic Ponderings

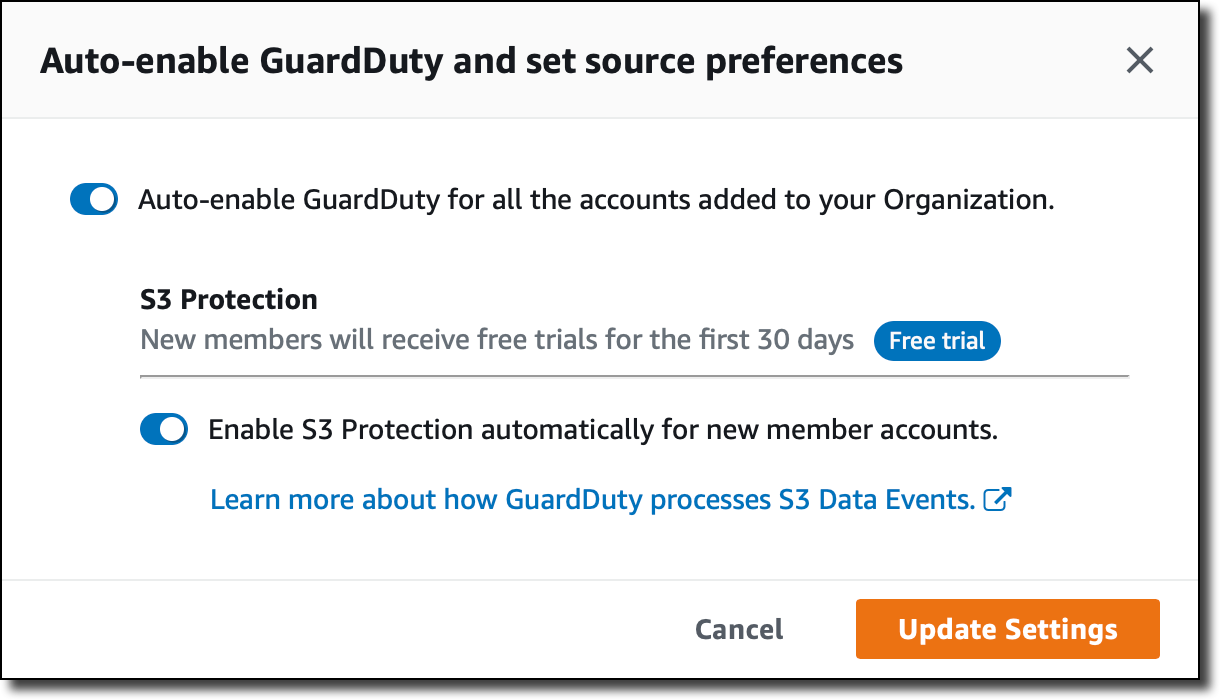
Strengthen the security of sensitive data stored in Amazon S3 by using additional AWS services | AWS Security Blog

How to use KMS and IAM to enable independent security controls for encrypted data in S3 | AWS Security Blog

S3 Antivirus Scanning with Lambda and ClamAV by Dennis Webb — AWS Cloud Expert and Slack Comedian | by Tim Meyer | FAUN Publication